Cybersecurity risk a primary buying consideration for Chief Supply Chain Officers

By 2025, 60% of supply chain organisations will use cybersecurity risk as a significant determinant in conducting third-party transactions and business engagements. As the surface area of digital supply chains expand, enhanced cybersecurity is a key theme that Chief Supply Chain Officers (CSCOs) will look to scale this year. “Our survey data has shown an […]
Retail and manufacturing sectors ‘most likely’ to be targeted by a cyber-attack

Health, education, retail, and manufacturing sectors continue to be particularly vulnerable to cyber attacks and data breaches, according to analysis of recently released 2021 ICO data. CybSafe analysed data from the Information Commissioner’s Office (ICO) – the UK’s independent body upholding information rights – following its previous analysis of ICO data for the first half […]
DHL, Amazon and DocuSign among most imitated brands in phishing emails
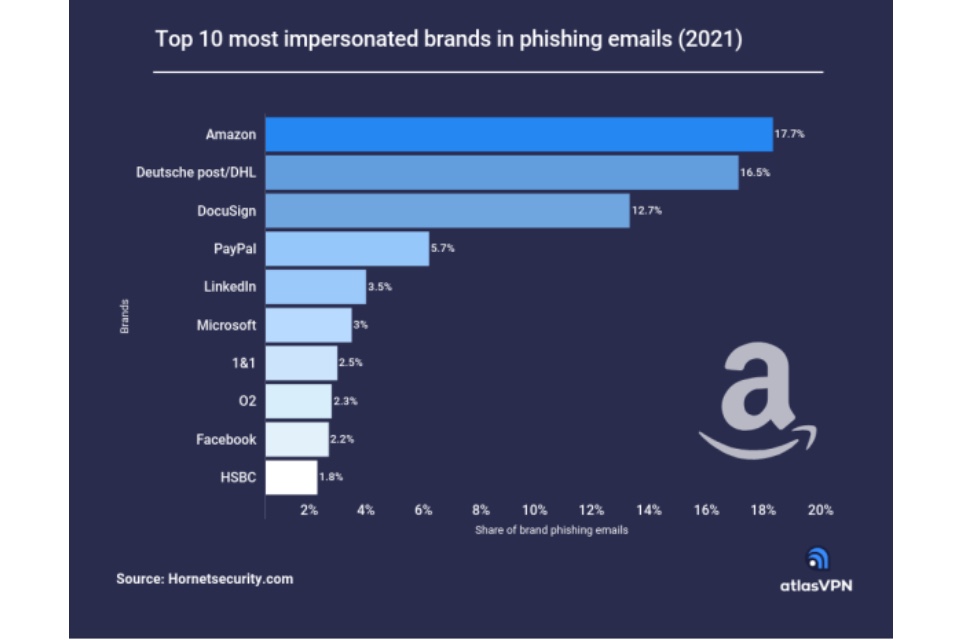
According to the data presented by the Atlas VPN team, Amazon topped the list as the most impersonated brand in email phishing attacks worldwide last year. In total, 17.7% of brand phishing emails used Amazon’s brand name. The trillion-dollar brand is closely followed by the world’s leading logistics company DHL and a cloud-based electronic signature technology […]

